15 Military codes that changed history
Throughout human history, the ability to communicate secretly has often meant the difference between victory and defeat. From ancient battlefields to modern warfare, military codes have shaped the course of nations and altered the fate of empires.
These encrypted messages have triggered wars, ended conflicts, and saved countless lives by keeping vital information from enemy hands. The art of military cryptography has evolved dramatically over the centuries, from simple letter substitutions carved into stone to complex machine-generated ciphers that required teams of mathematicians to crack.
Here’s a list of 15 military codes that didn’t just protect secrets—they fundamentally changed the trajectory of human history.
Caesar Cipher

Julius Caesar developed one of history’s most famous military codes around 50 BC, using a simple letter substitution method where each letter was shifted a fixed number of places in the alphabet. What made this cipher revolutionary wasn’t its complexity, but its systematic application across Roman military communications.
Caesar typically used a shift of three letters, so ‘A’ became ‘D’, ‘B’ became ‘E’, and so forth. Pretty straightforward stuff, really.
This encryption method helped coordinate Roman legions across vast distances and contributed to Caesar’s military successes in Gaul and beyond.
Scytale Cipher

The ancient Spartans used a device called the scytale, a wooden rod wrapped with parchment or leather strips to create transposition ciphers for military communications. Military leaders would wrap the strip around a rod of specific diameter, write their message along the length, then unwrap it to create seemingly random letters.
Only someone with a rod of identical thickness could decode the message. This cipher proved crucial during the Peloponnesian Wars, allowing Spartan commanders to coordinate strategies without revealing their plans to Athenian interceptors.
Like Go2Tutors’s content? Follow us on MSN.
Great Cipher of Louis XIV

Antoine Rossignol and his family created what became known as the Great Cipher for King Louis XIV of France. It remained unsolved from its initial use until 1890.
This sophisticated code used numbers to represent syllables rather than individual letters, making it nearly impossible to crack using traditional frequency analysis. An encrypted message from the time of the Man in the Iron Mask, decrypted just prior to 1900 by Étienne Bazeries, shed some light on the identity of that legendary prisoner.
The cipher’s strength helped France maintain diplomatic and military advantages for over two centuries—quite the return on investment for a royal cryptographer.
Vigenère Cipher

The Vigenère Cipher, published by Giovan Battista Bellaso but misattributed to French cryptologist Blaise de Vigenère, became the landmark polyphonic cipher of the 16th century. Unlike simple substitution ciphers, this method used a keyword to create multiple cipher alphabets, making frequency analysis much more difficult.
During the American Civil War, the military adapted this 15th-century cipher to create cipher disks for transmitting sensitive information via telegraph. Its polyalphabetic nature revolutionized military cryptography and influenced cipher development for centuries.
Zimmermann Telegram

In January 1917, British cryptographers in Room 40 deciphered a telegram from German Foreign Minister Arthur Zimmermann to the German Minister to Mexico, proposing a military alliance against the United States. The telegram offered Mexico the return of Texas, New Mexico, and Arizona in exchange for joining Germany if the United States entered World War I.
The decryption has been described as the most significant intelligence triumph for Britain during World War I and marked one of the earliest occasions when signals intelligence influenced world events. When published in American newspapers on March 1, 1917, it galvanized public opinion and helped push the United States into the war.
Like Go2Tutors’s content? Follow us on MSN.
Room 40 Operations

British Naval Intelligence, known as Room 40, successfully intercepted and decoded vast amounts of German communications during World War I. In October 1914, the Russian admiralty gave Room 40 a copy of the German naval codebook removed from a drowned sailor’s body from the cruiser SMS Magdeburg.
Talk about a stroke of luck. This intelligence coup, combined with stolen diplomatic codes, allowed Britain to read most German military and diplomatic traffic by 1917.
Room 40’s codebreaking capabilities provided crucial intelligence that influenced naval battles and diplomatic negotiations throughout the war.
MI-8 Black Chamber

When Ralph Van Deman established the War Department’s intelligence organization after the United States entered World War I, he created the Army’s first code and cipher bureau, known as MI-8 or the Black Chamber. Led by Herbert Yardley, MI-8 grew rapidly to 165 military and civilian personnel working in five subsections: Code and Cipher Solutions, Code and Cipher Compilation, Secret Inks, Shorthand, and Communications.
The organization revolutionized American cryptographic capabilities and laid the foundation for modern U.S. signals intelligence, processing over 100 classified messages daily during the war—no small feat for a brand-new operation.
Enigma Machine

The German Enigma cipher was possibly the most important codebreaking target of World War II, with its successful decryption by the Allies providing invaluable military intelligence throughout the war. The Enigma Machine had a series of scrambler disks with 26 letters, and by 1938, each machine had five scrambler disks, creating over 150 million million million possible combinations.
British cryptologists at Bletchley Park decrypted a vast number of Enigma messages, with the intelligence codenamed ‘Ultra’ providing substantial aid to the Allied war effort. Breaking Enigma shortened the war and saved countless Allied lives.
Like Go2Tutors’s content? Follow us on MSN.
Purple Cipher

A similar break into the most secure Japanese diplomatic cipher, designated Purple by the U.S. Army Signals Intelligence Service, started before the U.S. entered the war. On September 20, 1941, Genevieve Grotjan cracked the Japanese Purple machine code, giving the U.S. access to all of Japan’s diplomatic communications and insight into Axis thinking.
The Americans referred to intelligence resulting from Purple cryptanalysis as ‘Magic’. While this diplomatic intelligence didn’t warn of Pearl Harbor, it provided crucial strategic information throughout the Pacific War.
JN-25 Naval Code
U.S. Navy cryptographers, with cooperation from British and Dutch cryptographers after 1940, broke into several Japanese Navy crypto systems, including JN-25. The break into JN-25 famously led to the U.S. victory in the Battle of Midway.
Even so, the Chicago Tribune’s publication of this fact shortly after the battle could have compromised the entire operation. This codebreaking success demonstrated how signals intelligence could determine the outcome of major naval engagements and shift the balance of power in the Pacific.
Navajo Code Talkers

The U.S. Marine Corps used approximately 400 to 500 Native Americans whose primary job was to transmit secret tactical messages using codes built upon the Navajo language. The code proved so effective that a three-line message requiring 30 minutes to send using traditional methods could be encoded, transmitted, and decoded by Navajo code talkers in just 20 seconds.
At Iwo Jima, six Navajo code talkers working around the clock during the first two days sent over 800 messages without a single error. Their code was never broken and is the only spoken military code never to have been deciphered.
Like Go2Tutors’s content? Follow us on MSN.
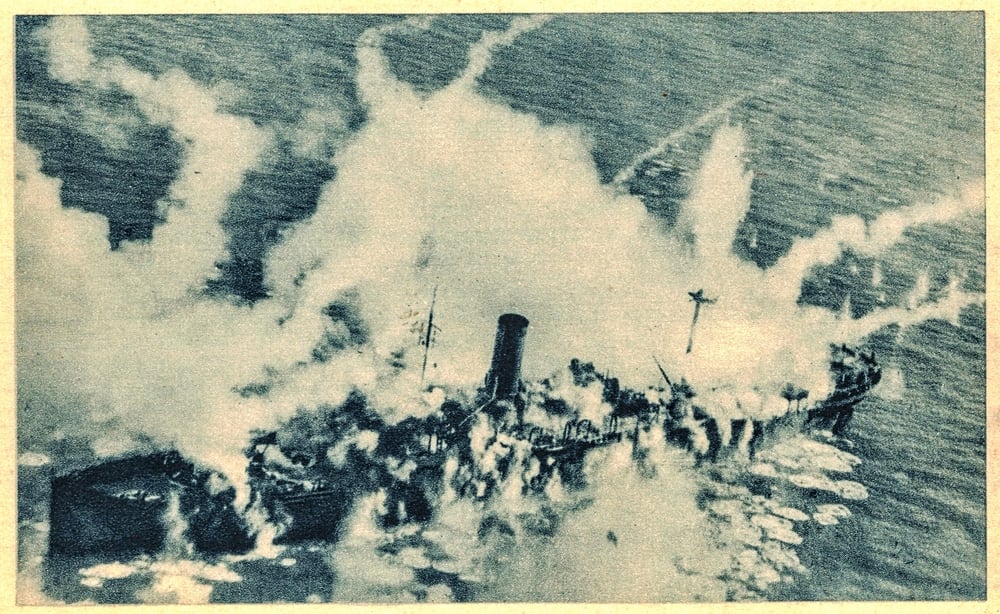
German Submarine Codes
On February 1, 1942, Germany changed its submarine communication code to a four-rotor Enigma cipher, temporarily blinding British codebreakers to German U-boat operations. This allowed German U-boat wolf packs freedom to roam the Atlantic, sinking American shipping faster than new vessels could be built.
The breakthrough came in late October 1942 when British sailors dove into freezing water to retrieve a weather cipher book from a sinking German submarine. Regaining the ability to read submarine communications proved decisive in winning the Battle of the Atlantic.
Operation Ultra

Intelligence from decrypted German communications, including Enigma and the Lorenz cipher, was eventually called Ultra and provided crucial strategic intelligence throughout World War II. At the end of the war, on April 19, 1945, Britain’s highest civilian and military officials were told they could never reveal that German codes had been broken.
Ultra intelligence influenced major Allied operations from D-Day planning to the North African campaign. The success of Ultra demonstrated how comprehensive signals intelligence could provide strategic advantages that fundamentally altered the course of a global conflict—and still influences modern intelligence operations today.
Cold War Diplomatic Codes

Following World War II, both superpowers developed increasingly sophisticated diplomatic and military codes to protect sensitive communications during the Cold War. The Venona project allowed U.S. cryptographers to decrypt Soviet diplomatic cables from the 1940s, revealing extensive Soviet espionage networks in America.
Meanwhile, sophisticated one-time pad systems and later computer-generated codes protected the most sensitive military communications. These encryption systems helped prevent misunderstandings that could have triggered nuclear conflict during tense standoffs like the Cuban Missile Crisis.
Like Go2Tutors’s content? Follow us on MSN.
Modern Military Encryption
Modern military ciphers have evolved to meet the complex demands of contemporary warfare, transitioning from traditional methods to advanced cryptographic systems like AES (Advanced Encryption Standard) and RSA algorithms. Digital encryption now protects everything from satellite communications to drone operations.
So today’s military forces can coordinate complex operations across global networks without fear of interception. These systems have revolutionized battlefield communications, enabling real-time intelligence sharing and precision strikes that have fundamentally changed the nature of modern warfare.
The Enduring Legacy of Secret Communications

From Caesar’s simple letter shifts to today’s quantum-resistant algorithms, military codes have consistently proven that information superiority can be just as decisive as superior firepower. As Brigadier General Marlborough Churchill predicted in 1919, ‘Code attack is indeed still in its infancy and capable of rapid and incalculable development.’
The evolution of military cryptography reflects humanity’s endless quest to protect secrets while simultaneously working to uncover those of others. Today’s cyber warfare and quantum computing represent the latest chapters in this ancient struggle, ensuring that the art of military codes will continue shaping history for generations to come.
More from Go2Tutors!

- 16 Historical Figures Who Were Nothing Like You Think
- 12 Things Sold in the 80s That Are Now Illegal
- 15 VHS Tapes That Could Be Worth Thousands
- 17 Historical “What Ifs” That Would Have Changed Everything
- 18 TV Shows That Vanished Without a Finale
Like Go2Tutors’s content? Follow us on MSN.