16 Military Codes That Were Never Broken by Enemies
Throughout history, the ability to communicate secretly has meant the difference between victory and defeat on the battlefield. Military forces have developed increasingly sophisticated ways to hide their messages from enemy eyes, creating codes so complex that some remain unbroken to this day. These cryptographic marvels protected crucial intelligence, saved countless lives, and changed the course of wars.
From ancient ciphers to modern encryption, these codes represent some of humanity’s most brilliant achievements in secrecy. Here is a list of 16 military codes that enemies never managed to crack.
Navajo Code Talkers

The Navajo language became one of the most effective military codes during World War II, stumping Japanese codebreakers completely. The U.S. Marines recruited hundreds of Navajo speakers who developed a complex system using their native language to transmit battlefield communications.
What made this code nearly impossible to break was that Navajo had no written form at the time, and fewer than 30 non-Navajo people worldwide could speak it fluently.
VENONA Project Encryption

Soviet intelligence used a theoretically unbreakable encryption system called the one-time pad for their most sensitive communications during the Cold War. Each message was encrypted using a unique key that was never reused, making it mathematically impossible to decrypt without the original key.
The system only became vulnerable when Soviet agents accidentally reused some key materials, but thousands of messages remained completely secure.
Like Go2Tutors’s content? Follow us on MSN.
PURPLE Diplomatic Code

Japan’s PURPLE machine created diplomatic codes that remained unbroken by most Allied forces throughout World War II. This electromechanical cipher device generated incredibly complex encryptions that protected Japan’s most sensitive diplomatic communications.
While American cryptographers eventually cracked PURPLE through painstaking analysis, many other nations never managed to break these codes during the war.
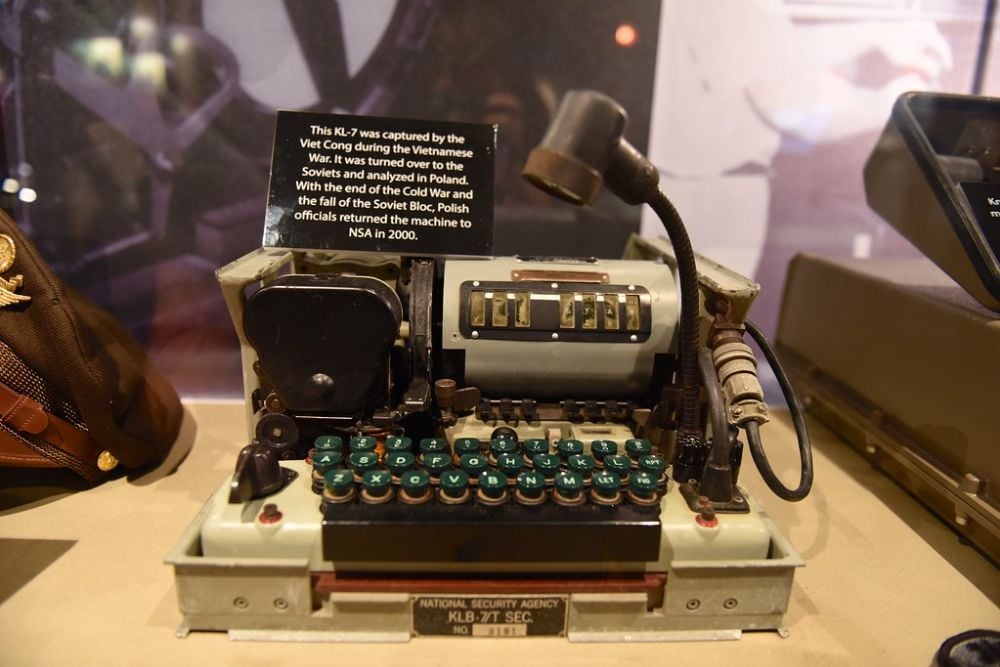
KL-7 ADONIS System

The U.S. military’s KL-7 ADONIS cipher machine produced codes that foreign intelligence services never successfully broke during its operational period from the 1950s to the 1980s. This rotor-based encryption device created over 10 million possible key combinations, making brute force attacks practically impossible with the technology available at the time.
The system’s security came from its complex mechanical design and frequent key changes.
Soviet Vernam Cipher
The Soviet military employed a version of the Vernam cipher that created truly random encryption keys for their most critical communications. This system generated keys using physical processes that produced genuine randomness, not just mathematical pseudo-randomness.
Enemy cryptographers couldn’t predict or recreate these keys because they were based on unpredictable physical phenomena like radioactive decay.
Like Go2Tutors’s content? Follow us on MSN.
British TYPEX Codes

Britain’s TYPEX cipher machine generated military codes that Axis powers never managed to crack during World War II. This electromechanical device was essentially an enhanced version of the famous Enigma machine, but with additional security features that made it far more resistant to codebreaking attempts.
The machine used multiple rotors and complex wiring that created billions of possible encryption combinations.
Cherokee Code System

Similar to the Navajo code talkers, Cherokee speakers served as military communicators using their native language as an unbreakable code. The Cherokee writing system, developed by Sequoyah in the 1820s, was completely unknown to enemy forces who encountered these transmissions.
The complexity of the language structure and its unfamiliarity to non-Cherokee speakers made these communications completely secure.
SIGSALY Voice Encryption

The SIGSALY system encrypted voice communications so effectively that enemy forces never broke a single conversation during World War II. This massive machine, weighing over 50 tons, digitized speech and then encrypted it using random noise patterns.
The receiving station needed an identical copy of the noise pattern to decrypt the message, making interception useless without the proper keys.
Like Go2Tutors’s content? Follow us on MSN.
M-209 Tactical Codes

The M-209 cipher machine created tactical field codes that remained secure throughout World War II despite heavy use by American forces. This portable mechanical device could generate over 100 million different key combinations, making it practically impossible for enemy cryptographers to break messages in the short time they remained tactically relevant.
The machine’s compact size and reliability made it perfect for frontline communications.
Soviet One-Time Tape System

The Soviet military used physical tape systems that generated truly random encryption keys for their most sensitive operations. These tapes contained sequences of random numbers that were used only once and then destroyed, making the encrypted messages mathematically unbreakable.
The system required perfect synchronization between sender and receiver, but when properly implemented, it provided absolute security.
Choctaw Code Communications

Choctaw speakers served as code talkers during World War I, creating the first successful Native American military code system. German intelligence services did not know this Native American language and couldn’t find anyone who could translate the intercepted messages.
The Choctaw code system was so effective that it inspired the larger Navajo code talker program in World War II.
Like Go2Tutors’s content? Follow us on MSN.
ADFGX Cipher Variant

A specialized variant of the ADFGX cipher used by certain military units remained unbroken throughout World War I despite intensive enemy codebreaking efforts. This system combined substitution and transposition techniques in ways that created multiple layers of encryption.
The cipher’s complexity grew exponentially with each additional step, creating codes that were beyond the computational abilities of the era.
Lakota Military Communications

Lakota speakers provided secure communications for American forces using their native language as an unbreakable military code. The grammatical structure of Lakota differs dramatically from European languages, making it impossible for enemy linguists to decipher even if they managed to record transmissions.
The language’s complex verb conjugations and unique syntax created natural encryption that no foreign military could penetrate.
Soviet Fish Cipher

The Soviet Union developed a cipher system nicknamed ‘Fish’ by Western intelligence that protected their highest-level military communications throughout the Cold War. This system used multiple encryption layers and frequently changed keys to create messages that remained secure even when intercepted.
The cipher’s mathematical complexity required computational power that exceeded what most intelligence agencies possessed at the time.
Like Go2Tutors’s content? Follow us on MSN.
German Diplomatic Red Code

Germany’s diplomatic Red Code system protected certain high-level communications that Allied forces never successfully decrypted during World War II. This cipher used a complex book code system combined with additional encryption layers that created messages too difficult to break with wartime resources.
The system required specific editions of books that served as the foundation for the encryption process.
SIGABA Machine Codes

The American SIGABA cipher machine created military codes that no enemy force ever broke during its operational lifetime from the 1940s through the 1960s. This electromechanical device used multiple rotors and complex stepping patterns that generated encryption far more sophisticated than the famous German Enigma machine.
The system’s security came from its unpredictable rotor movements and frequent key changes.
Echoes Across Time

These unbroken codes represent more than just technical achievements—they show how creativity and cultural knowledge can become powerful weapons in warfare. Many of these systems succeeded not because of mathematical complexity alone, but because they drew on unique cultural resources like Native American languages or combined multiple encryption techniques in innovative ways.
Today’s digital encryption continues this tradition, protecting everything from military communications to online banking with mathematical principles that would have seemed like magic to codebreakers of the past.
Like Go2Tutors’s content? Follow us on MSN.
More from Go2Tutors!

- 16 Restaurant Chains That Went Too Fast
- 12 Things Sold in the 80s That Are Now Illegal
- 15 Strange Things People Have Tried to Ban (And Failed)
- 16 Collectibles People Tossed Out Too Soon
- 17 Myths from Your Childhood That Were Actually Based on Real Things
Like Go2Tutors’s content? Follow us on MSN.



