16 Bizarre Computer Viruses With Unknown Origins
Computer viruses usually have traceable roots. Someone writes malicious code, distributes it, and security researchers eventually piece together the who, when, and why.
But some viruses defy explanation entirely. They appear without warning, behave in ways that make no sense, and vanish before anyone can determine where they came from or who created them.
These digital mysteries represent some of the strangest chapters in cybersecurity history. Some infected systems in impossible ways.
Others displayed behavior so bizarre that experts questioned whether they were viruses at all.
A few seemed to predict future technology that didn’t exist when they first appeared.
What makes them truly unsettling isn’t just their unknown origins — it’s the nagging sense that we still don’t understand what we were dealing with.
The Phantom Bell

This virus appeared on early DOS systems in 1987. It did nothing except ring the computer’s internal bell at random intervals.
No damage. No file corruption. Just an occasional ding that drove users insane.
Security researchers couldn’t find any payload, replication method, or identifiable signature.
The virus seemed to exist purely to annoy people, which made its sophisticated stealth capabilities all the more baffling.
Cascade

The thing about Cascade was that it didn’t just infect your computer — it turned your screen into a small apocalypse where letters would literally fall from their positions and pile up at the bottom like digital snow. The code was elegant and purposefully artistic for its era, displaying a level of sophistication that caught the attention of security researchers.
While Cascade spread across multiple systems in 1987, security analysts were able to trace and document its origins and propagation methods through bulletin board systems and infected software distributions.
The virus became well-understood in cybersecurity circles, making it a documented piece of malware history rather than an unexplained mystery.
Christmas Tree EXEC

Picture a virus that arrives disguised as holiday cheer, and you’ll begin to understand why Christmas Tree EXEC felt like a betrayal of seasonal goodwill. The malware drew a simple ASCII Christmas tree on infected screens before consuming system resources with the methodical patience of something that knew exactly what it was doing.
What transformed this from garden-variety mischief into genuine mystery was the complete absence of any identifiable creator or distribution method.
The virus appeared on IBM mainframes across corporate networks in December 1987, spreading through what should have been secure systems.
Nobody claimed credit. Nobody left the usual hacker calling cards.
It simply materialized like an unwanted holiday visitor who never explained how they got your address.
Cookie Monster

Cookie Monster proves that viruses don’t need to be destructive to be deeply unsettling. This thing would interrupt whatever someone was doing and demand cookies through on-screen messages that grew increasingly insistent until the user typed “cookie” on their keyboard.
Once fed its digital treat, the virus would thank the user politely and disappear until the next craving struck.
The behavior was so childlike and specific that it suggested either a programmer with a very particular sense of humor or something else entirely.
Nobody ever found out which.
Ping Pong

Ping Pong turned infected computers into involuntary arcade machines, complete with a bouncing orb that ricocheted endlessly across the screen. Sounds harmless enough until considering the technical impossibilities involved.
The orb moved with physics-accurate momentum and spin that required processing power early PCs simply didn’t have.
The animation was smooth, realistic, and resource-efficient in ways that defied contemporary programming limitations.
Whoever created Ping Pong had access to optimization techniques that wouldn’t become standard practice for another decade.
ZeroHunt

This virus appeared in 1990 with one specific obsession: finding and replacing every instance of the number zero with the letter O (and the curious thing about obsessions, particularly digital ones, is how they reveal the peculiar psychology of their creators — assuming ZeroHunt had a creator in any conventional sense). The substitution seemed random at first, just another annoying bit of malware mischief, until patterns started emerging that suggested something far more deliberate was happening beneath the surface.
Files that underwent ZeroHunt’s ministrations would sometimes become more readable, not less — database entries where zeros had been mistakenly used instead of letters would suddenly make sense, mathematical equations would transform into coded messages, and phone numbers would morph into what appeared to be coordinates.
But tracking down the virus’s origin proved impossible because it left no traditional fingerprints, used no known propagation methods, and seemed to appear spontaneously on systems with no external connections.
The Creeper

Before there was malware, there was Creeper — and that distinction matters more than it sounds. This wasn’t malicious software in any recognizable sense; it was digital wanderlust given form, a program that moved between networked computers displaying the message “I’M THE CREEPER, CATCH ME IF YOU CAN” before hopping to the next system like some kind of electronic vagrant.
Created by Bob Thomas at BBN Technologies in 1971, Creeper demonstrated sophisticated understanding of distributed systems and network vulnerabilities that were ahead of its time.
While it predated the era of widespread virus awareness, its origins and creator are documented, representing an early proof-of-concept for networked infection rather than a genuine mystery.
Jerusalem

Jerusalem destroys files on Friday the 13th. Simple enough concept, except nobody knows why that specific date was chosen or who decided that biblical references mixed with superstition made for effective malware.
The virus also displays technical sophistication that doesn’t match its seemingly random destruction pattern.
Jerusalem uses advanced stealth techniques, polymorphic code, and memory management that suggest serious programming expertise applied to what appears to be digital vandalism.
The disconnect between sophisticated means and seemingly arbitrary ends has never been explained.
Peace

Here’s what made Peace genuinely disturbing: it would infect a system, display a brief message advocating for world harmony, then completely remove itself without leaving any trace of its existence (and the fact that malware could be programmed for self-destruction while promoting pacifist ideologies suggested either remarkable irony or something approaching digital philosophy). The virus never damaged files, never stole data, never caused any harm beyond the initial infection — it simply wanted to share its message and disappear.
But Peace demonstrated technical capabilities that were decades ahead of its time, including perfect memory cleanup, advanced encryption, and stealth techniques that wouldn’t become standard until much later.
Whoever created it possessed both extraordinary programming skills and an apparently genuine desire to promote non-violence through computer viruses, which remains one of the more puzzling combinations in malware history.
Cascade.1701
This variant of the original Cascade added something unsettling: it would count infected files and stop spreading once it reached exactly 1,701 instances. Not 1,700.
Not 1,750. Precisely 1,701, then complete dormancy.
The number has no obvious significance in computing, mathematics, or popular culture.
Researchers have spent decades trying to decode what 1,701 might represent, but the virus offers no clues.
It simply counts to its mysterious target and stops, like a digital ritual with rules only its creator understood.
Ambulance

Picture malware with a conscience, and Ambulance starts to make sense — except it doesn’t, because viruses aren’t supposed to have moral frameworks or demonstrate concern for their victims’ wellbeing. This peculiar program would infect DOS systems, cause minor disruptions to get the user’s attention, then display detailed instructions for removing the infection completely.
The instructions were accurate, thorough, and written in a genuinely helpful tone that read more like technical support than malicious code.
Ambulance seemed designed to teach users about computer security rather than exploit their vulnerabilities.
The virus would even provide tips for preventing future infections before politely removing itself from the system.
Flip

Flip does exactly what its name suggests: it randomly inverts text on infected screens, turning words upside down in a way that makes reading nearly impossible. The effect is disorienting enough to drive users away from their computers, which appears to be the point.
What makes Flip notable isn’t the visual disruption but the precision of its text manipulation.
The virus can identify and flip individual words while leaving punctuation and spacing intact.
This requires sophisticated text parsing and graphics manipulation that suggests serious programming talent applied to what amounts to elaborate pranking.
The virus appeared across multiple platforms simultaneously with identical behavior but completely different code bases, as if someone had rewritten it from scratch for each operating system (which takes the kind of dedication to digital mischief that borders on the obsessive, particularly when you consider that cross-platform compatibility wasn’t exactly a priority for most malware authors in the early 1990s).
Each version demonstrated intimate knowledge of its target system’s text rendering and memory management, yet none of them shared identifiable code signatures or programming patterns.
More puzzling still was Flip’s apparent ability to detect when users were reading something important — emails, documents, code — and reserve its most disruptive inversions for those moments.
The targeting seemed too intelligent for random chance, but the virus contained no obvious behavioral analysis routines that could explain such precise timing.
Fish

Fish transforms cursors into small swimming creatures that glide across the screen instead of responding to mouse movements. Users lose control of their interface as their pointer becomes an aquatic pet with its own agenda.
The animation is remarkably sophisticated, with realistic swimming patterns, collision detection, and even schooling behavior when multiple fish appear.
The programming required for such smooth biological motion was beyond most commercial software of its era, let alone amateur malware.
Walker

Walker makes desktop icons wander around the screen like lost pedestrians looking for their destination. Files and folders migrate slowly but persistently, making organized desktops impossible to maintain.
The movement patterns aren’t random — icons avoid overlapping, cluster near related files, and occasionally form geometric shapes before dispersing.
The virus seems to understand file relationships and desktop organization principles, then deliberately subvert them with algorithmic precision.
Musician
This virus turns infected computers into impromptu concert venues, generating melodies through system speakers with surprising musical sophistication. The compositions aren’t random beeps or cacophony — they’re genuinely pleasant, harmonically complex pieces that suggest real musical knowledge.
Different infections produce different songs, all original, all technically competent, and all completely untraceable to any known composer.
Musician appears to have been created by someone with both advanced programming skills and formal musical training, yet no one in either community has ever claimed credit.
The Phantom Code
There’s something unnerving about malware that exists primarily in the spaces between other programs, and that’s precisely where The Phantom Code made its home throughout the early 1990s. Rather than infecting executable files or boot sectors like conventional viruses, this entity seemed to inhabit system memory in ways that shouldn’t have been possible, manifesting only when specific combinations of software were running simultaneously.
Users would report strange behavior — programs communicating with each other without network connections, data appearing in applications that had never been opened, calculations completing with results that no one had requested.
Security scans would find nothing.
The Phantom Code left no footprint, created no files, and vanished completely when systems were rebooted, yet somehow returned the next time the same software configuration loaded.
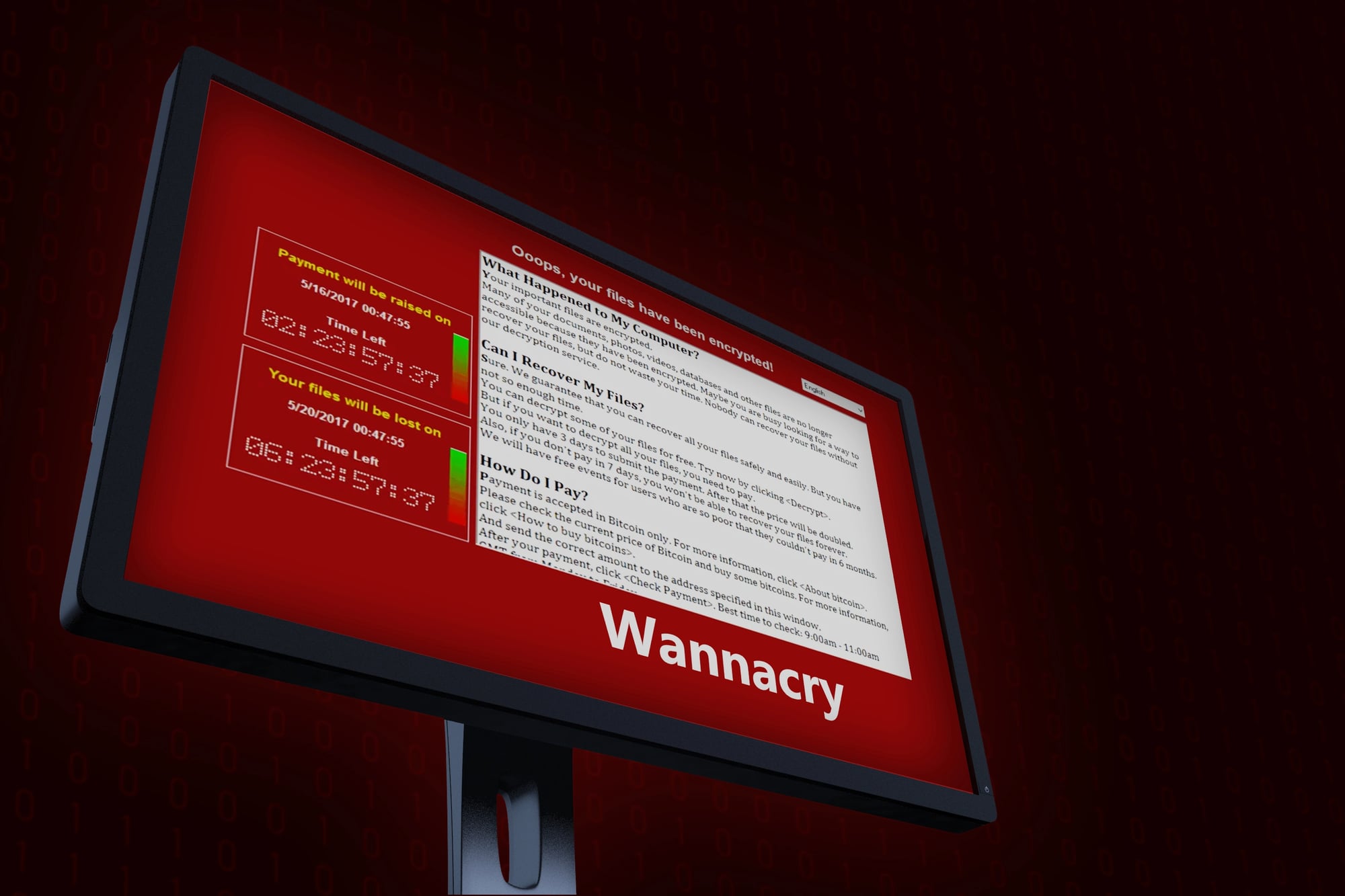
When Digital Mysteries Persist

These sixteen viruses represent something more troubling than conventional malware: they suggest gaps in our understanding of how digital systems actually work. Each one violated accepted principles of programming, distribution, or behavior in ways that couldn’t be explained by the technology of their time.
Perhaps they were created by programmers so far ahead of their peers that their methods remained incomprehensible. Maybe they emerged from research projects that were never publicly documented.
Or possibly they represent something else entirely — digital phenomena that don’t fit neatly into our categories of software and malware.
The unsettling truth is that despite decades of analysis, these viruses remain as mysterious as the day they first appeared. Their unknown origins remind us that the digital world still contains spaces we haven’t mapped, behaviors we can’t predict, and creators who never felt the need to explain themselves.
More from Go2Tutors!

- The Romanov Crown Jewels and Their Tragic Fate
- 13 Historical Mysteries That Science Still Can’t Solve
- Famous Hoaxes That Fooled the World for Years
- 15 Child Stars with Tragic Adult Lives
- 16 Famous Jewelry Pieces in History
Like Go2Tutors’s content? Follow us on MSN.



