18 Everyday Objects That Are Actually Spyware
You probably don’t think twice about the gadgets scattered around your home. They sit quietly on shelves, counters, and desks, making life easier while blending into the background.
But many of these devices watch, listen, and record more than you realize. They collect data about your habits, conversations, and movements—then send it somewhere else.
The line between convenience and surveillance has become impossibly thin. What feels like a helpful tool often doubles as a data collection machine.
And most people have no idea how much information these objects gather or where it goes.
Smart TVs

Your television knows what you watch, when you watch it, and how long you stay glued to the screen. Many models have built-in cameras and microphones that capture more than just your viewing preferences.
Some manufacturers admit they collect voice data and share it with advertisers. The screen you trust for entertainment tracks your entire household.
It remembers which apps you open, which streaming services you prefer, and even which ads you pause on. This information builds a detailed profile of your interests and behavior.
And turning off certain features doesn’t always stop the data collection—it just makes it less obvious.
Voice Assistants
Smart speakers sit in your kitchen, bedroom, or living room, waiting for commands. But they’re always listening, even when you’re not talking to them.
These devices need to hear the wake word, which means they’re constantly monitoring every conversation in range. Voice recordings often get stored on company servers.
Tech companies review these clips to improve their algorithms, but that means real people hear snippets of your private conversations. And if someone hacks the system, they gain access to months or years of audio from inside your home.
Fitness Trackers

That little band on your wrist knows more about you than your doctor. It tracks your heart rate, sleep patterns, location, and daily activities.
Some models even monitor stress levels and reproductive cycles. This health data gets synced to apps that share information with third parties.
Insurance companies, advertisers, and data brokers pay good money for insights about your physical condition and lifestyle. The terms of service you scrolled past give these companies permission to use your most personal information however they want.
Smart Thermostats

A thermostat that learns your schedule sounds convenient. But it also knows when you’re home, when you leave, and which rooms you use most often.
This creates a detailed map of your daily routine. Energy companies access this data to analyze usage patterns.
And because these devices connect to your Wi-Fi, they can serve as entry points for hackers. A compromised thermostat can reveal when your house sits empty—information that’s valuable to more than just marketers.
Security Cameras

Cameras meant to protect your home often do the opposite. Cloud-connected models upload footage to remote servers where it gets stored indefinitely.
Company employees can access these videos, and so can anyone who exploits a security flaw. Some camera manufacturers faced scandals when their employees were caught watching private footage.
The cameras in your bedroom, bathroom, or nursery might have more viewers than you planned. And facial recognition technology can identify everyone who appears in the frame, building a database of your visitors.
Baby Monitors

Parents buy these devices for peace of mind, not realizing they’re inviting strangers into the nursery. Many baby monitors have weak security that makes them easy targets for hackers.
Stories of creeps talking to children through compromised monitors appear in the news regularly. The video and audio feeds from these devices sometimes get intercepted and shared online.
And even without hackers, the manufacturer’s own servers store this intimate footage. Your child’s first steps and bedtime routines become data points in someone else’s database.
Smart Refrigerators

A refrigerator with a touchscreen and internet connection does more than keep your food cold. It tracks what you buy, how often you open the door, and which items you consume most frequently.
Some models have cameras inside that photograph the contents every time you close the door. This grocery data gets analyzed and sold to food companies and retailers.
Your eating habits become marketing intelligence. And because these appliances connect to your home network, they can be compromised to access other devices or spy on your kitchen conversations.
Robotic Vacuums

That little robot mapping your floors creates a detailed blueprint of your home’s layout. It knows where your furniture sits, which rooms you have, and how you move through the space.
Advanced models use cameras and sensors to navigate, capturing images of your belongings in the process. These maps get uploaded to company servers where they’re stored and analyzed.
Some companies have considered selling floor plans to advertisers or other third parties. And if your vacuum gets hacked, someone else can see inside your home and know your entire floor plan.
Smart Light Bulbs

Even your light bulbs spy on you now. Connected bulbs track when you’re awake, which rooms you occupy, and your daily patterns.
They communicate with apps that collect location data and usage statistics. This information reveals more than you’d think.
Light patterns can indicate how many people live in a home, their sleep schedules, and when the house sits empty. And because these bulbs connect through your Wi-Fi, they can be exploited to access your network and other devices.
Connected Doorbells

Video doorbells record everyone who approaches your home—whether you know them or not. They capture faces, license plates, and conversations happening on your porch.
This footage gets stored on company servers and sometimes shared with law enforcement without your knowledge. Some doorbell companies have partnerships with police departments, giving authorities access to neighborhood camera networks.
Your doorbell becomes part of a surveillance system that extends far beyond your property line. And the constant recording means your neighbors and delivery workers all end up in a database they never agreed to join.
Streaming Devices

Roku boxes, Amazon Fire sticks, and similar gadgets track every show, movie, and video you watch. They monitor how long you watch, when you pause, and which content you skip.
This viewing data builds a profile that advertisers use to target you across different platforms. These devices also have microphones for voice control.
And just like smart speakers, they’re always listening for commands. The remote control in your hand collects data about your TV habits and sends it to multiple companies who profit from knowing your entertainment preferences.
Smart Plugs

A device that lets you control outlets from your phone seems harmless. But smart plugs track which devices you use, when you use them, and for how long.
They know your daily routine based on when you turn things on and off. This usage data reveals patterns that advertisers and data brokers find valuable.
And because these plugs connect to your home network, they can be compromised to spy on other devices or disrupt your power supply. Something as simple as controlling a lamp becomes a surveillance tool.
E-Readers
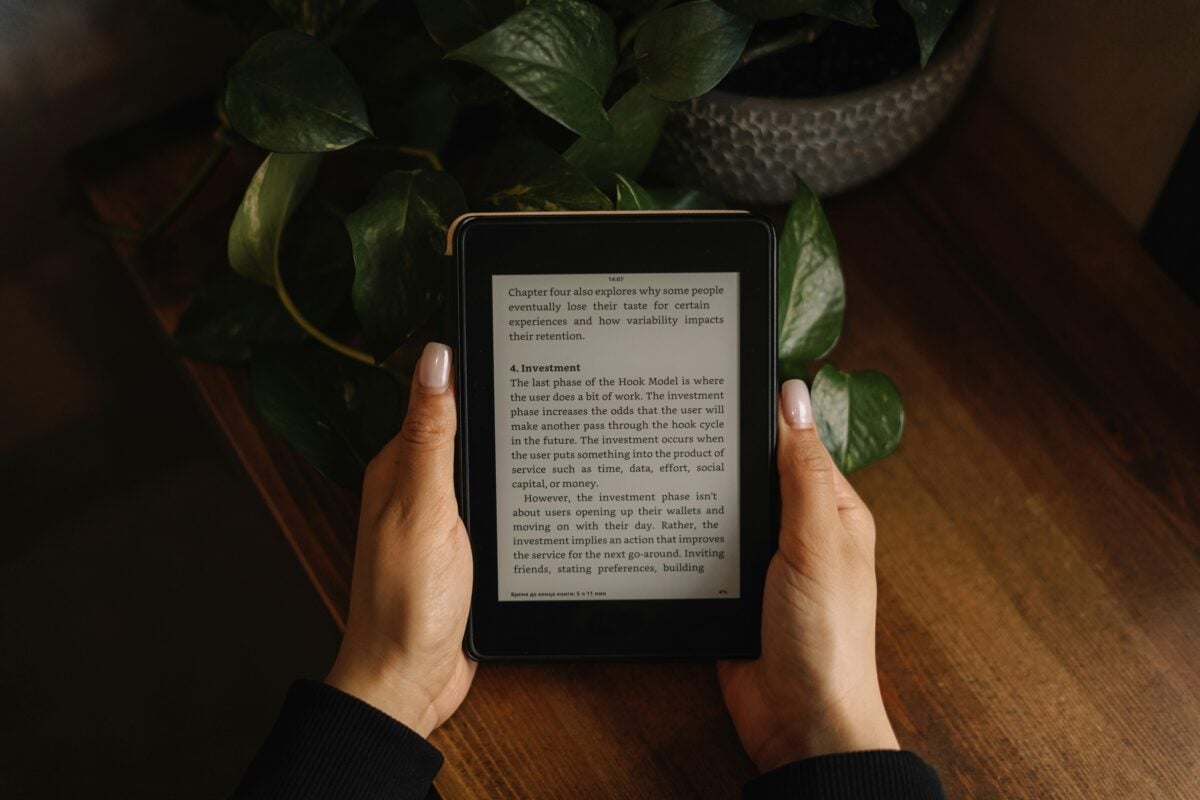
Digital book readers track every page you read, how fast you read it, and which passages you highlight. They know which genres you prefer, which books you finish, and which ones you abandon.
Some models monitor how long you spend on each page. This reading data gets analyzed to recommend new books and target ads.
But it also reveals your interests, political views, and personal struggles based on what you choose to read. The private act of reading becomes another source of data collection.
Gaming Consoles

PlayStation, Xbox, and other gaming systems track far more than your high scores. They monitor how long you play, which games you choose, and who you interact with online.
Built-in cameras and microphones capture your reactions and conversations during gameplay. This data gets used for marketing and game development, but it also builds detailed profiles of players.
And when consoles connect to your home network, they can access other devices and collect information beyond just gaming activity. Your entertainment system becomes a surveillance hub.
Smart Toothbrushes

Yes, even your toothbrush can spy on you. Connected toothbrushes track how long you brush, which teeth you focus on, and how often you use it.
They sync this data to apps that share it with dental insurance companies and health researchers. This seems innocent until you realize your brushing habits become part of your health profile.
Insurance companies can use this data to adjust rates or deny coverage. And like all connected devices, smart toothbrushes can be hacked to access your home network or personal information.
Connected Cars

Modern vehicles are computers on wheels, and they collect massive amounts of data. They track where you drive, how fast you go, your braking patterns, and how aggressively you accelerate.
GPS systems know every location you visit and how long you stay there. This driving data gets shared with insurance companies, who use it to calculate rates and assess risk.
Some car manufacturers sell location data to advertisers and data brokers. And built-in microphones can record conversations inside the vehicle, adding another layer of surveillance to your daily commute.
Smart Scales

Bathroom scales that connect to your phone track more than just your weight. They monitor body fat percentage, muscle mass, bone density, and other health metrics.
This information syncs to apps that share it with health companies and researchers. Your most private health data becomes part of larger databases used for medical studies and insurance calculations.
And because these scales connect to your network, they can be compromised to access other devices. Stepping on the scale each morning feeds data to dozens of companies you’ve never heard of.
Digital Picture Frames

Connected photo frames show your memories, yet they also send those pics to faraway computers. These devices notice which images you pick, how frequently you swap them out, plus who’s actually in the shots.
Software that spots faces figures out exactly who is pictured there. This builds a record of your connections, relatives, plus key life events.
Since these devices require Wi-Fi to update pictures, they link to your router – opening doors for hackers. Those precious snapshots turn into bits of info stored somewhere you don’t control.
The Quiet Watchers in Your Home

These things seem like they’re part of daily living now. Yet behind the ease lies a hidden price few notice.
Instead, every gadget gathers data on your private moments – sending it off, saving copies without asking. While offering speed and access, they quietly track what you do. The data keeps moving – streaming from your house to company systems, then bouncing off to strangers you don’t even know.
When it’s loose, you can’t track who views it, what they do with it, or which corners of the web it lands in. Things meant to simplify daily routines end up shredding any chance at real privacy.
You can’t dodge spying completely – this is life when everything links up. Yet you still pick what tech enters your space, along with who gets permission.
Devices won’t stop evolving – they’ll link tighter, act sharper, watch closer. So here’s the real deal: will you just keep handing over control?
More from Go2Tutors!

- The Romanov Crown Jewels and Their Tragic Fate
- 13 Historical Mysteries That Science Still Can’t Solve
- Famous Hoaxes That Fooled the World for Years
- 15 Child Stars with Tragic Adult Lives
- 16 Famous Jewelry Pieces in History
Like Go2Tutors’s content? Follow us on MSN.



