16 Unsolved Internet Puzzles Baffling Modern Hackers
The internet holds secrets. Some hide behind layers of encryption that would take centuries to crack. Others sit in plain sight, their meaning lost to time and circumstance.
These aren’t corporate data breaches or government conspiracies — they’re puzzles left by individuals who wanted to test the limits of collective intelligence. And yet, despite armies of hackers, cryptographers, and curious minds working together, sixteen digital riddles remain unsolved, their creators’ intentions as mysterious as their solutions.
Cicada 3301
The most famous unsolved puzzle appeared in January 2012 as a simple image posted to 4chan. “Hello. We are looking for highly intelligent individuals.”
What followed was a month-long treasure hunt spanning multiple continents, requiring knowledge of cryptography, steganography, ancient literature, and number theory. Participants decoded messages hidden in images, solved puzzles referencing William Blake and ancient runes, and even received physical mailings containing more clues.
Two more cycles appeared in 2013 and 2014, each more complex than the last. A few participants claim to have reached the final stage — but if they did, they’ve never spoken publicly about what they found.
The trail goes cold every time.
The Kryptos Fourth Panel
Standing outside CIA headquarters in Langley, Virginia, is a copper sculpture containing four encrypted messages. Three of the four panels have been solved over the past three decades, revealing poetic references to archaeological discoveries and the act of decryption itself.
The fourth panel — just 97 characters long — has resisted every attempt at decryption since 1990. Even with hints from the sculptor Jim Sanborn (who revealed that characters 64-69 spell “BERLIN”), the message remains locked.
The CIA has never officially acknowledged whether their own analysts have cracked it, which somehow makes it more maddening.
John Titor’s IBM 5100 Reference

In 2000 and 2001, someone claiming to be a time traveler from 2036 posted detailed messages on internet forums about his mission to retrieve an IBM 5100 computer from 1975 (he mentioned a hidden feature in the 5100 that wasn’t publicly documented until years later, which struck many as oddly prescient — even unsettling, given how specific and accurate this detail turned out to be). And the predictions he made about future events: some missed entirely, others landed with uncomfortable precision, creating this patchwork of hits and misses that keeps people analyzing his posts decades later.
But what really bothers people isn’t what he got right or wrong. It’s how he vanished completely in March 2001, exactly when he said he would.
The mystery isn’t whether time travel is real — it’s who John Titor actually was, and how someone in 2000 could have known about that IBM feature when the information wasn’t supposed to exist yet.
The Voynich Manuscript Digital Reproductions

The original Voynich Manuscript sits in Yale’s Beinecke Library, its 15th-century pages filled with unknown script and impossible botanical illustrations. Yet scattered across various corners of the internet are high-resolution digital copies containing subtle differences — extra marginalia, variant spellings, pages in different orders. Some of these differences appear to be scanning artifacts. Others look intentional.
Someone has been systematically creating and distributing modified versions of the Voynich digital reproductions. The alterations follow no obvious pattern, and tracking their origin leads nowhere.
Whether this represents an elaborate hoax or a coded message hidden within an already indecipherable text remains unknown.
UVB-76 Number Station Audio Files
Since 1973, a Russian shortwave radio station has broadcast a monotonous buzzing tone interrupted occasionally by number sequences and Russian voice recordings. Known as UVB-76 or “The Buzzer,” the station’s purpose remains officially unacknowledged.
But the real puzzle lives in the audio files that circulate online. Embedded within seemingly routine recordings of The Buzzer are digital artifacts that suggest steganographic encoding.
Spectral analysis reveals patterns that shouldn’t exist in analog radio transmissions — patterns that look suspiciously like encrypted data. Whether these artifacts are introduced during digital conversion or represent genuine hidden messages, no one has successfully decoded them.
The Lake City Quiet Pills Mystery

Forums and encrypted chat rooms contain oblique references to something called “Lake City Quiet Pills” — usually just the abbreviation LCQP. The references appear in contexts suggesting it’s either a code name for a covert operation or a digital marketplace for something highly illegal.
Yet despite years of investigation by internet sleuths, no one has definitively identified what LCQP actually represents. The mystery deepened when researchers found references to LCQP in financial records and shipping manifests that seem completely unrelated to the online discussions.
Either it’s an elaborate red herring, or multiple groups are using the same code phrase for entirely different purposes.
A858DE45F56D9BC9

One Reddit user, A858DE45F56D9BC9, posted nothing but strings of hexadecimal characters for over four years. The posts followed no obvious schedule, contained no apparent pattern, and generated thousands of pages of attempted analysis from cryptography enthusiasts.
Some users claimed to find hidden messages; others insisted the posts were meaningless. The account went silent in 2016, having posted over 2,000 cryptic messages.
Despite exhaustive crowd-sourced analysis involving steganography, frequency analysis, and every known cipher technique, no consensus emerged about what — if anything — the messages actually said.
The Max Headroom Broadcast Signal Intrusion
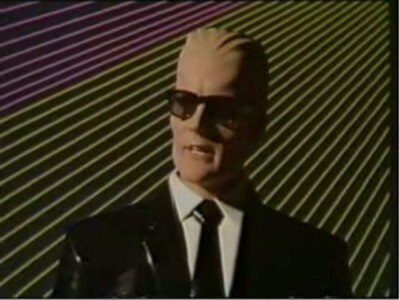
On November 22, 1987, someone hijacked two Chicago television stations for a total of about 90 seconds, broadcasting a bizarre video of someone in a Max Headroom mask delivering cryptic messages over static. The perpetrator was never identified, making this one of the few successful broadcast intrusions to remain completely unsolved.
But the real puzzle isn’t the identity of the hijacker — it’s the garbled audio during the broadcast. Enhanced digital analysis of surviving recordings suggests there might be additional audio tracks layered beneath the obvious dialogue, possibly containing encoded information.
The enhancement techniques available in 1987 wouldn’t have revealed these potential hidden layers, leaving open the possibility that the broadcast carried more information than anyone realized at the time.
Markovian Parallax Deniability Posts

Across multiple platforms — Reddit, Twitter, obscure forums — automated accounts occasionally post long, seemingly random strings of text under variations of the phrase “Markovian Parallax Deniability.” The posts read like corrupted philosophical treatises: grammatically coherent but semantically nonsensical.
They appear just frequently enough to maintain visibility but not so often as to trigger spam filters. The phrase itself is a computer science reference to plausible deniability in encrypted communications.
Whether these posts represent a broken AI experiment, an art project, or a genuine attempt at steganographic communication remains unclear. The accounts posting them show no other activity and never respond to direct questions.
The Wyoming Incident

In 2006, someone uploaded a video to various file-sharing platforms claiming to show a “lost” local television broadcast from Wyoming that had supposedly aired years earlier. The video contains disturbing imagery and what appears to be encrypted data hidden in the visual static.
Despite being obviously fabricated as an art project or alternate reality game, the video contains genuinely encrypted elements that have never been solved. Analysis of the static patterns reveals mathematical sequences that don’t match standard television broadcast interference.
Someone embedded real cryptographic puzzles within this fictional “found footage” — and then never provided any solution or claimed credit for the puzzle elements.
Sad Satan Game Code

In 2015, a YouTuber claimed to have received a link to a mysterious video game called “Sad Satan” through the dark web. The game consisted of walking through surreal, disturbing environments with hidden audio and visual elements.
The original version of the game was never publicly released, leaving only corrupted copies that might not represent the original puzzle. Hidden within the game’s audio files are reversed speech samples, frequency-modulated tones, and spectrographic images that appear to contain encoded information.
Whether the original creator intended these as puzzles or whether they’re simply atmospheric elements designed to create unease, no one has successfully decoded whatever messages might be hidden in the game’s files.
11B-X-1371

A video posted to YouTube in 2015 shows someone in a plague doctor mask and medieval clothing performing ritualistic gestures while holding up cards with symbols and numbers. The video description contained only coordinates pointing to a location in Poland where someone had reportedly left a cryptic message on a piece of paper.
The symbolism in the video draws from multiple sources — alchemical texts, mathematical notation, and what appear to be invented glyphs. Despite extensive analysis of the symbols, gestures, and audio (which contains layered whispers and tones), no coherent message has been extracted.
The video feels like an elaborate puzzle, but if there’s a solution, it remains hidden.
The Babington Plot Cipher Variants
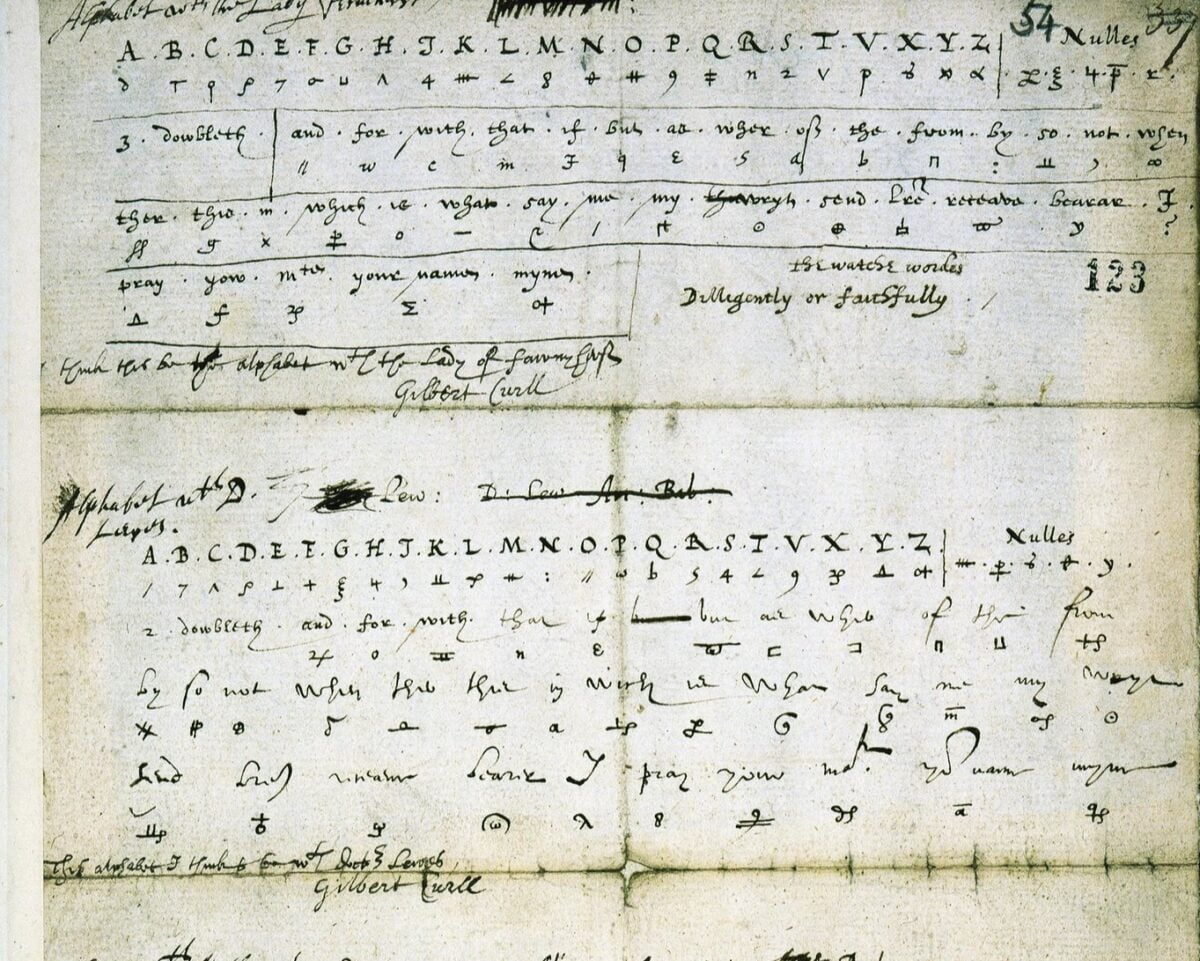
Historical records show that Mary Queen of Scots and her conspirators used a substitution cipher for their correspondence during the Babington Plot of 1586. The cipher was cracked at the time, leading to Mary’s execution.
But scattered across various historical archives and digitization projects are documents containing similar-looking ciphers that don’t match the known Babington cipher key. These variant documents have been largely ignored by historians, who assume they’re either corrupted copies or different ciphers entirely.
But cryptographic analysis suggests they might be layered encryptions — messages encoded using the known Babington cipher and then encrypted again using a different method. No one has successfully decoded these double-encrypted historical documents.
Deep Web Chess Notation

Various dark web forums contain long posts consisting entirely of chess notation — strings of moves like “1.e4 e5 2.Nf3 Nc6” that appear to describe complete games. The games, when played out, are strategically nonsensical.
Pieces are sacrificed randomly, obvious checkmates are ignored, and the games often end abruptly without resolution. But the move sequences contain patterns that suggest steganographic encoding.
Certain piece movements occur far more frequently than random chance would suggest, and the games often contain exactly 64 moves — matching the number of squares on a chess board. Whether these represent encoded communications between specific parties or are simply spam designed to waste analysts’ time remains unknown.
The Tengwar Twitter Bot
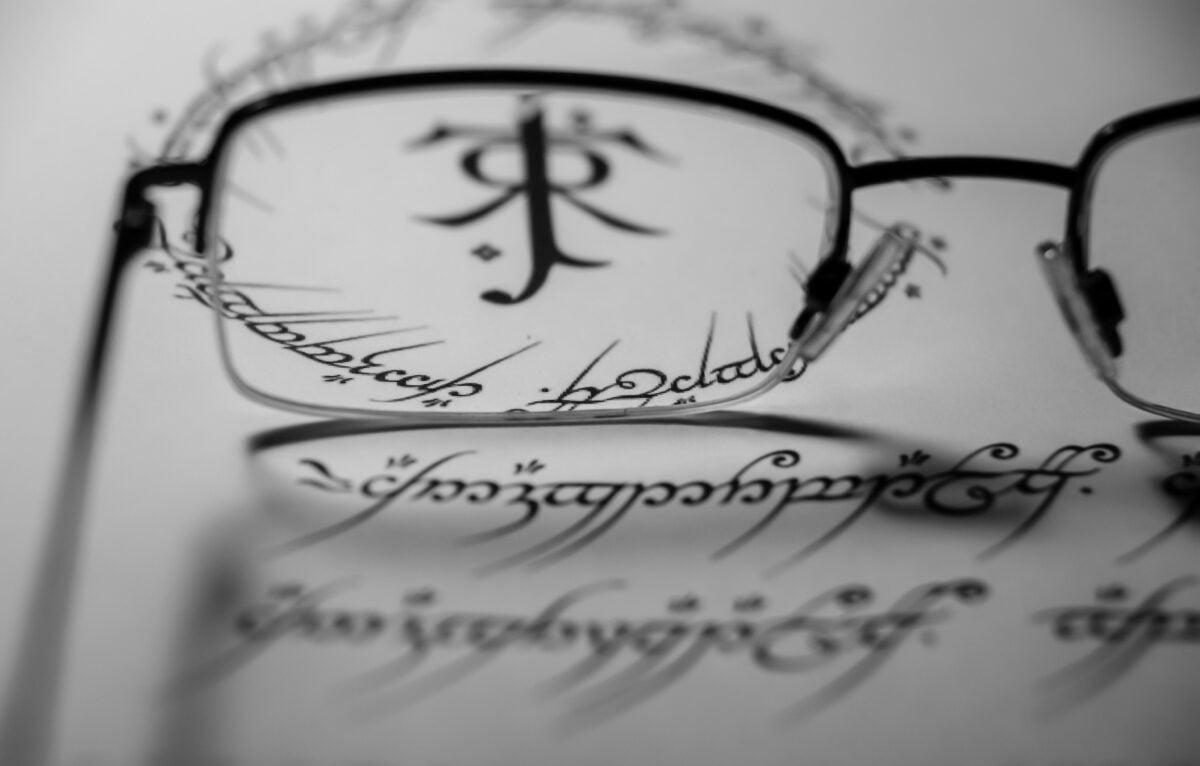
An automated Twitter account posts daily messages written in Tengwar, the Elvish script created by J.R.R. Tolkien for his Middle-earth stories. The messages appear to be transliterations of English text into Tengwar characters, but when decoded, they produce mostly gibberish — almost-coherent sentences that read like corrupted poetry or philosophical fragments.
The account has posted consistently for over six years without ever acknowledging questions or providing context. Some of the decoded messages contain references to real places and historical events, while others seem entirely fictional.
Whether the account represents an art project, a coded communication system, or simply a broken algorithm attempting to generate meaningful text, no one has determined its actual purpose.
Project Azorian Documentation References
Declassified CIA documents about Project Azorian (the 1974 mission to recover a sunken Soviet submarine) contain footnote references to supplementary documentation that doesn’t appear to exist in official archives. The reference numbers follow CIA classification systems, but when researchers have requested these specific documents through FOIA, they’re told no such documents can be located.
More puzzling, some of these phantom reference numbers have appeared in unrelated internet discussions about cryptography and puzzle-solving. Whether someone is using legitimate-sounding document numbers as code phrases, or whether there’s actually missing documentation being referenced in underground communities, remains unclear.
The Digital Archaeology of Unanswered Questions

These puzzles represent something uniquely modern: mysteries that exist because the internet allows them to persist indefinitely. Unlike historical ciphers or ancient riddles that fade into obscurity, digital puzzles can be copied, shared, and analyzed by unlimited numbers of people for unlimited amounts of time.
And yet, persistence doesn’t guarantee solutions. What’s fascinating isn’t that these puzzles remain unsolved — it’s that they continue to attract serious attention years or decades after their initial appearance.
Each represents a kind of digital archaeology, where layers of analysis and speculation accumulate around the original mystery until the investigation becomes as interesting as whatever answer might eventually emerge. The internet has created a new category of puzzle: one that’s designed not necessarily to be solved, but to endure.
More from Go2Tutors!

- The Romanov Crown Jewels and Their Tragic Fate
- 13 Historical Mysteries That Science Still Can’t Solve
- Famous Hoaxes That Fooled the World for Years
- 15 Child Stars with Tragic Adult Lives
- 16 Famous Jewelry Pieces in History
Like Go2Tutors’s content? Follow us on MSN.



